LDAP/ADS login service
The ldap-login-service is provided as an OSGi bundle, which may be activated by
obr:addurl http://maven.clazzes.org/repository.xml
obr:deploy gwt-ldap-login-service
The maven artifact is:
<groupId>org.clazzes.gwt</groupId>
<artifactId>gwt-ldap-login-service</artifactId>
Functionality
The LDAP login service authenticates against users in an ADS domain or against users in an LDAP server configured for an individual domain.
The LDAP login service might need credential to bind to an LDAP Server before actually searching a user name based on the given userAttribute.
For ADS Servers a non-search policy is implemented, which tries to bind using a principal in the form user@domain.
Configuration
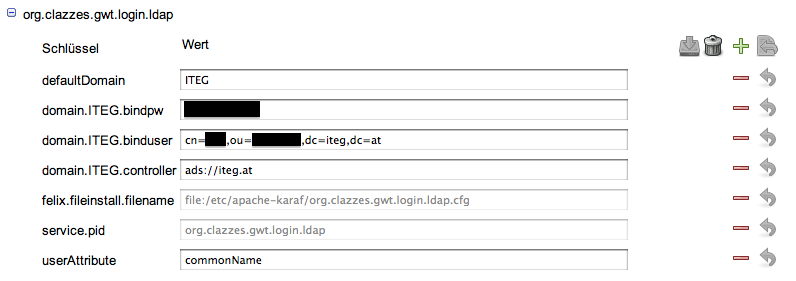
The LDAP login service may be configured using the OSGi configuration PID
org.clazzes.gwt.login.ldap
as shown in the following gwt-config-manager screenshot
The configuration values are
| Key | Default Value | Description |
|---|---|---|
| defaultDomain | The domain to use for principals, which do not contain a domain. | |
| maxRetries | 3 | The maximal number of retries before a user agent is blocked. |
| sessionTimeout | 180 | The session timeout in Minutes to set on the HTTPSession upon successful authentication. |
| userAttribute | samAccountName | The LDAP attribute to use for finding a DN for a given user. |
| domain.<domain>.controller | The server to contact. Supported URL schemes: ldap, ldaps, ads. See below | |
| domain.<domain>.authMethod | searchAndBind | The method for authenticating a user. Supported methods: searchAndBind, bindAds. |
| domain.<domain>.bindpw | The password used for binding before searching the given user in the domain <domain>. Applies only to the authMethod 'searchAndBind'. | |
| domain.<domain>.binduser | The DN used for binding before searching the given user in the domain <domain>. Applies only to the authMethod 'searchAndBind'. |
There might be multiple domains in a configuration.
Controller Schemes
The URL schemes for a domain controller are ldap, ldaps and ads.
The ads URL scheme for the URL ads://mydomain.com undertakes a lookup for the
TXT _ldap._tcp.mydomain.com
DNS record and the uses the returned LDAP server as if the ldap or ldaps URI scheme has been specified.